September 23, 2019
Why Risk Based Testing Is Your Best Bet to Deliver Stable Software?
This article highlights the importance of risk based testing and how it helps in delivering reliable and more stable software.
Risk is any uncertain, unlikely event with a positive or negative impact on the success of the project. The unpredictable events can impact the business, cost, product quality, and delivery timeliness.
Risk based testing (RBT) is an approach to check application likelihood of failures. This testing method is used to test the scenarios to check their impact on business. The RBT method prioritizes the modules and functions based on their likelihood of errors to remove critical bugs.
Any critical bug found at the production stage can lead to dissatisfied customers; badly impact their experience and cause business loss.
Risk based testing justified the efforts, which focus on the possible areas with a high probability of loss in the software.
This testing approach also ensures bugs found by the end-user leaves no impact on application results or user experience.
In this article, you will learn-
- When to use Risk Based Testing?
- What is the Risk Management Process?
- How to Perform Risk Based Testing?
- What are the Benefits of Using Risk Based Testing?
- How to Implement Risk Based Testing in Agile and DevOps?
- Example of Risk Based Testing
When to use Risk based testing?
- It is challenging to test the entire software exhaustively, so it is vital to select the most important sections to ensure adequate testing.
- This testing technique is preferred when the team has time, resource, and budget constraints.
- The technique is followed by a risk-based analysis to evaluate system vulnerability.
- It is also used to evaluate critical aspects of business and defect prone areas.
What is the Risk management process?
- Risk-based testing focuses on finding risk factors related to software. First, factors are identified, and then their categories are created based on their likelihood and impact. Risk is identified through various means such as conducting workshops, brainstorming, Delphi technique, cause, and effect diagram, RCT analysis, and interviews of subject matter experts.
- A risk identification register is maintained that tracks and monitors all types of risk. It checks the threats and opportunities of the project. Risk breakdown structure finds the most risk-prone areas and monitors their risk over time.
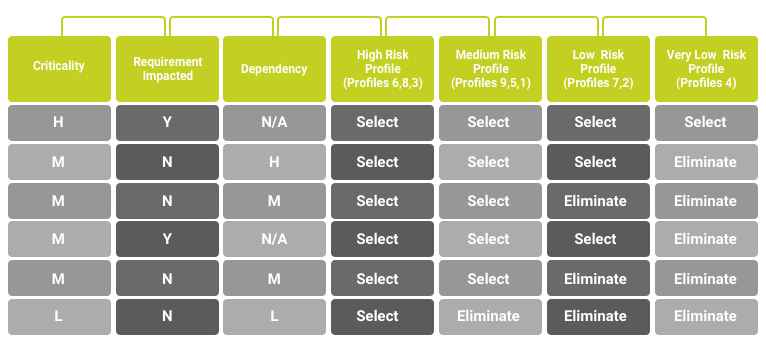
- After finding the optimal test suites for execution, the levels of optimization are decided through a sample of risk table. Based on the table below the test cases can be selected or eliminated based on their risk profile. This rule table helps in optimizing the test cases for execution.
- A risk assessment also helps in designing strategies and test cases based on the identification of risk factors.
- Risk analysis is used to filter and analyze the risk based on their impact on the business. A risk analysis template or matrix is created to define the probability vs. impact of the risk.
- Risk mitigation activities involve the set of activities required to eliminate the risk to lessen the impact.
- A risk contingency plan defines the backup plans and worst-case scenarios that could be performed on the occurrence of any unpredictable event.
- Monitoring and control involve tracking, monitoring new risk, the previous risk, and identifying the potential risk to define the reasons to change, execute, and monitor risk triggers.
Roles and responsibility chart at various levels in RBT process
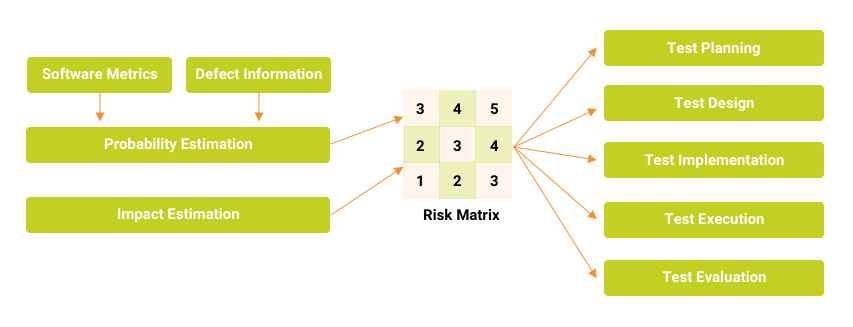
Test planning: The test manager decides the number of test cycles and strategy based on RE value. Manager now has more information about quality and focus areas.
Test design: Test cases are now designed to mitigate the risk. The information is used to design risk-based test cases.
Test Execution: The test cases are executed in RE order where the importance is given to functionalities that are likely to fail.
How to perform risk based testing?
The process of risk-based testing uses risk as a primary parameter to evaluate all the steps in the testing process. The testing process includes test planning, test design, test implementation, test execution, and test reporting.
Step 1
The stages of the testing process are ranked based on their intensity and the riskiest area of failure. The test cases are differentiated as high value and low value based on their priority. These test cases are created to test product features, functionalities, user stories. These steps are performed at the initial stage of the risk analysis before we start any risk based testing.
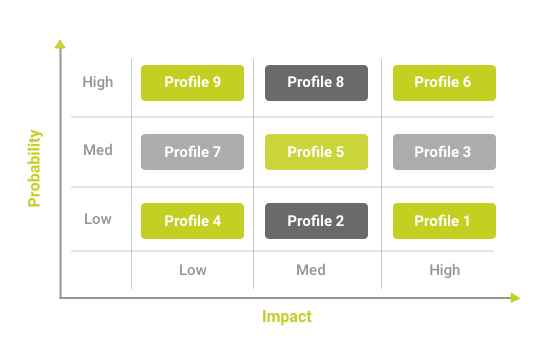
A 3*3 grid is created to perform the risk analysis. This risk analysis is used to evaluate each functionality, non-functionality, and related test cases. It measures their likelihood of failure. The functionalities are provided risk exposure value based on its complexity, cost, size, quality.
Step 2
The test cases are marked in the quadrants of a 3*3 grid-based structure based on the probability of failure and its impact. The test cases are marked as dots in various quadrants. The right corner of the grid depicts high likelihood and failure. The lower bottom left of the corner represents the high-value test and low-value test.
Step 3
Once you have the grid ready with test cases positioning based in their category. The test cases are provided numbers 1 to 5 to display their priorities. Numbering will help testers to get a list of priority. The one assigned 1 is of the highest importance and others will rank 2,3,4, and 5.
Step 4
This helps to sort out the best test cases to manage the software as per their priority numbers. The high priority will execute the first test cases thoroughly. Any risk identified before the test executions schedule is capable of reducing slippage from the development side. The test manager ensures testing before the promised timeline to ensure minimum risk and high quality.
What are the benefits of using risk based testing?
- It improves application quality by resolving bugs.
- The risk matrix helps in evaluating the highest likelihood of defects, which reduces time to fix critical bugs.
- It improves the overall process by streamlining strategies, directions and more focused on problem areas.
- It also monitors the risk to understand the status of the project and its quality.
- It also maps the product risk to the requirement gaps.
- It reduces the time to find and fix remaining bugs as the most critical bugs are minimized.
- The team can execute priority-based test cases that improve quality.
- Problem finding is easy and convenient through evaluating test cases.
- Projects can define when to stop testing in the project.
How to implement risk based testing in Agile and DevOps?
- Agile and DevOps focus on automating everything and test continuously and repeatedly.
- The priority levels of test cases help in quick manual testing, thus sparing time for automated testing. It saves time and resources.
- RBT approach helps in effectively creating the test cases and scenarios based on the risk factor on functionalities.
- A risk-based approach defines the high-risk areas in the software to detect bugs earlier and allow them to fail as early as possible to fix them. This concept is also called Fail Fast.
- The agile and DevOps approach is customer-oriented, the risk-based approach emphasizes on improving customer experience.
Example of Risk Based Testing
Let’s take an example of an Application Under Test (AUT) that is due for release and there is very less time left. The risk based testing approach is used to find critical bugs and release the software on time with high quality.
Step #1: Risk Identification
Identify all the major functional areas of the software and making a list of it.
Step #2: Risk Assessment
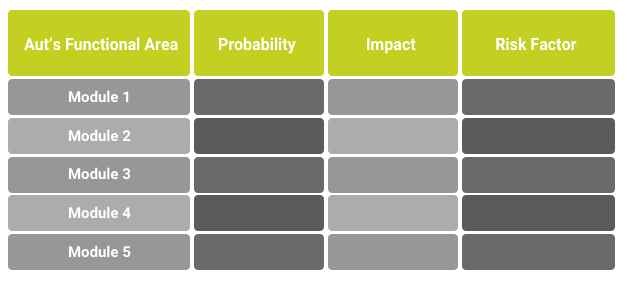
The possible list of risks against functionality is listed in tabular format and a number is assigned to all items. A priority number is also provided to them. Each risk and its impact is decided and matched.
The typical method is to assign the ratings. For example, the probability of occurrence of risk can take values from 1 to 5. The value 1 indicates a low risk (not and 5 being high (most likely to happen).
Similarly, Impact can also be assigned a 1-5 rating. The value 1 indicates low impact (even if this risk does materialize, the loss is minimum) and 5 being the high impact (huge losses).
Step #3:
Make a table and circulate it to all the team reps- Dev, BA, Client, PM, QA and anyone else relevant.
Step #4:
Ask each team member to fill in the values based on their rating for probability and impact.
Since the probability and impact values are numeric it will make the calculating of the “Risk Factor” value easy.
Risk factor = Probability X Impact. The higher the risk factor, the serious the problem is.
An example:
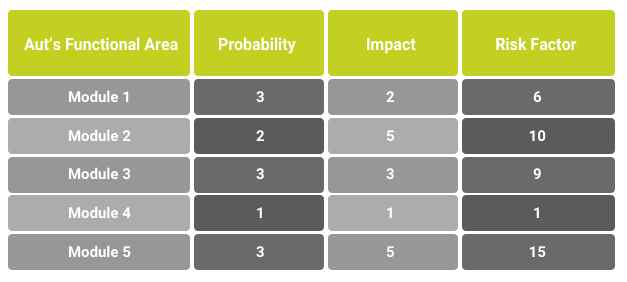
Please note that at this point, this is simply the outcome of one team’s rating. For a project where 5 different teams are involved the QA team would end up with 5 different tables.
Step #5:
Take an average of the Risk factor values. For example, if there are 5 teams, for each module, add all the risk factor values and divide it by 5. This is the final value we are going to deal with. Say, these are the averaged risk factors:
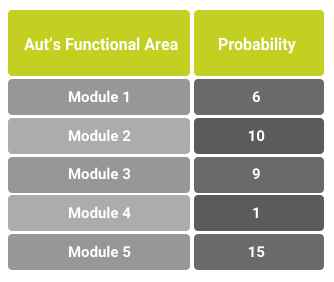
The more the risk factor, the more that module has to be tested.
So, Module 5 and 2 are most crucial for the success of the business.
Step #6:
Risk Mitigation Plan – Now, this is the step that changes from Project to Project. We have identified that modules 5 and 2 are the ones that need to be concentrated on most.
Examples of the plan could be:
Modules 5 and 2 will be tested thoroughly by making sure all the test cases related to them are tested. The other modules will be tested on an exploratory basis.
Modules 5 and 2 are going to be tested first and then depending on the time available.
Once a plan is made, all the teams reach an agreement and follow it to test the product keeping into account the risk factor.
Conclusion
Risk based testing helps teams in setting priorities and quick testing during tight schedules. Testers can use risk-based analysis to identify high-risk user stories to test first. Risk-based testing improves resource allocation and optimizes technical resources based on quality and usability perspective.
Share article